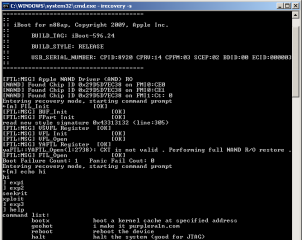
Obviously notorious George Hotz has managed to get all 7 SPUs of the Playstation 3’s CPU under his control. This means although he cannot access the CPU’s root key, he now can decrypt everything that’s going thru these SPUs like datastreams of (encrypted) commercial games.
The PPU is higher on the control chain then the SPUs. Even if checks were to be added to, for example, verify the hypervisor before decrypting the kernel, with clever memory mappings you can hide your modified hypervisor.
In the meantime another hacker going under the nick XorLoser has released a more detailed manual of how to use GeoHot’s exploitation files and how to do the glitching.
Besides that XorLoser maintains a plugin for reverser’s beloved Interactive Disassembler (IDA) that contains special PPC instructions for Xbox360 and PS3.
Congratulations to GeoHot. Kudos fly out to XorLoser.
Links
» GeoHot: On Isolated SPUs…
» XorLoser: PS3 Exploit – Software…
» XorLoser: PS3 Exploit – Hardware…
» XorLoser: PS3 and Xbox360 IDA PlugIn…
» Hex-Rays.com: IDA Pro…