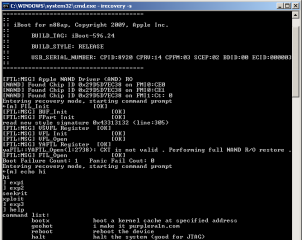
Notorious XorLoser has fully rewritten GeoHot’s PS3 glitch attack programs, that allow more convenient exploiting. He names it XorHack.
It allows you to call lv1 syscalls (level 1 system calls) from a normal (userspace) program. It also lets you run the software required when triggering the PS3 exploit from a normal userspace program. To give an example of how it can be used I have included the following example programs:
- ps3exploit – Runs the software required to exploit the ps3, it loops a number of times which can be specified as a parameter. (This still must be used along with the “button pressing”, it will not exploit the PS3 via software alone).
- dumphv – Dumps the hypervisor to a file in the current directory.
- dumpbl – Dumps the bootloader to a file in the current directory.
- dumprom – Dumps the system rom to a file in the current directory.
Links
» XorLoser: XorHack – The PS3 Exploit Toolkit…
» GeoHot: Here’s Your Silver Platter…
Picture is courtesy of XorHack…